For the newscast, we were given a large list of different ciphers that we had to choose from. We chose one called the scytale cipher. A cipher is an algorithm that is used to perform encryptions on messages for others to see, without people from the outside understanding what it means.
The scytale is a cipher is a piece of paper wrapped around a rod or stick or something firm to hold it in place, then write a message and unwrap it.
In the video, we explained very well how the cipher works, as well as why it was used. It is one of the easier ciphers to solve. Another thing that we talked about in the video is why the ciphers were so important. They were so important because, at the time, it was difficult to communicate without others knowing what you were saying.
Overall, what I learned from this newscast is that there are a lot of ways to communicate while still having your message encrypted. To add to this is that it was really fun to learn about different types of ways of communication and how people use different types of encryption to send messages back and forth between people.
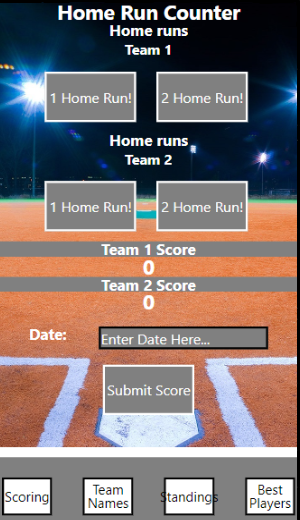
In this project, I made an app that tracked the score of two different baseball teams. On the first page of the program, you can add 1 or 2 points to a selected team’s score based on whether they get 1 or more points, and you can increase the score by 1 or 2. Below this, it shows the score of both teams and will update if you increase the points for each team. Just below that, it shows a text input where you can put in the date that the game occurred, and then click the submit button to submit the score so it will be saved.
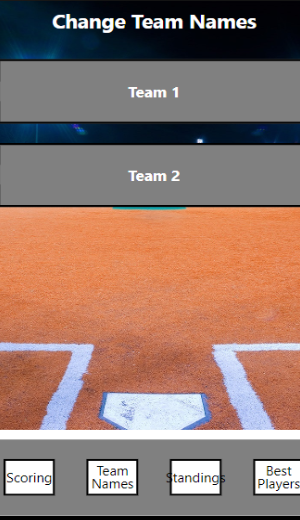
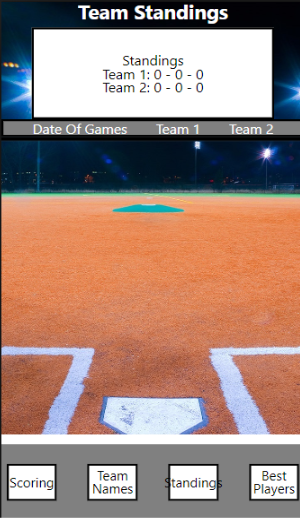
On the second page of the app, you can click on either team1 or team2 and change the names of either one to whatever name you would like. On the 3 pages of the app, it displays the ratio between the two teams, and it shows the number of wins, losses, and ties. Below this, it will show the date on which the games happened and the score of each team for that game.
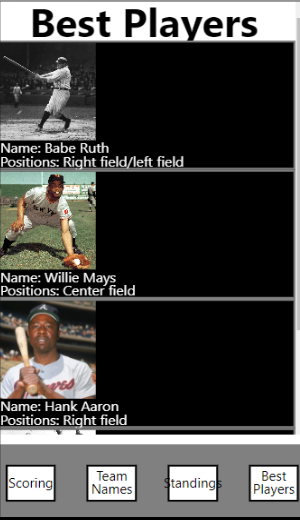
Finally, on the last page, it prints out all of the greatest baseball players of all time based on their statistics. This was done using mapping, and it will just change the information of each player, but repeats the same styling, and the information that is provided is a picture of the player, as well as their name and the position that they played.
After making this whole app, I have learned a lot of different things. To make a lot of the things that are in the app it took many different lessons to make the app work in different ways some of these many different lessons are styling the components, styling text, buttons, text boxes images, flex layouts, text inputs, states, mapping, and touchable highlights just to name a few and with all of these skills together it helped me make this app.
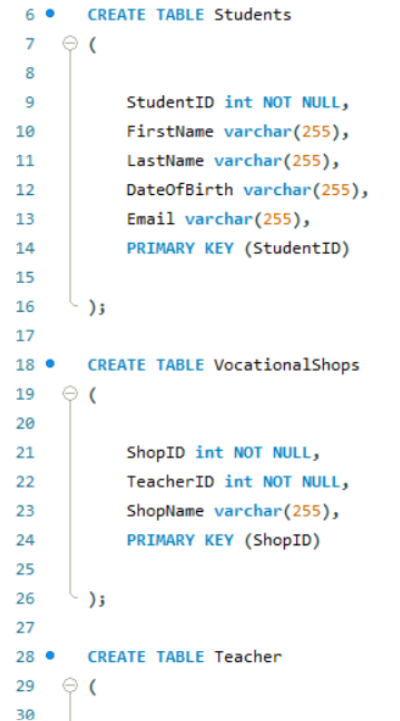
In this assignment, the goal is to create a database that will store all of the information of students who go to a selected vocational school. The point of this database is a place to store all information about the vocational school, meaning from students’ names or IDs all the way to teachers’/shop id, or names as well.
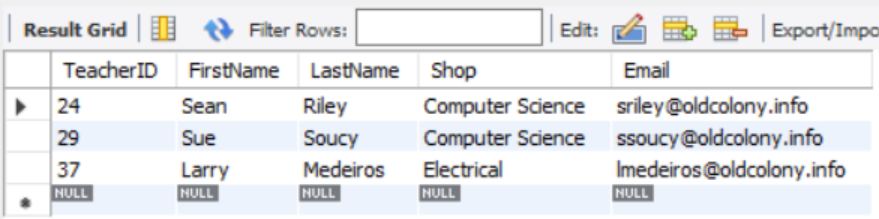
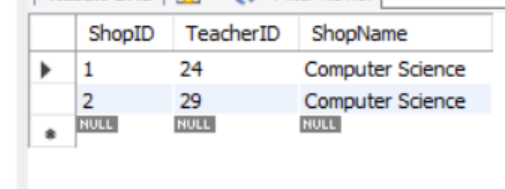
This will be done by firstly making three different tables, the first table being a collection of students and will include the following information: StudentID, FirstName, LastName, DateOfBirth, and lastly email. The following table would be “vocationalshops” in this table, it would take in the information of: ShopID, ShopName, ShopRoom, TeacherID. And the very last table would be a teacher’s table that would hold: TeacherID, FirstName, LastName, Shop, Email.
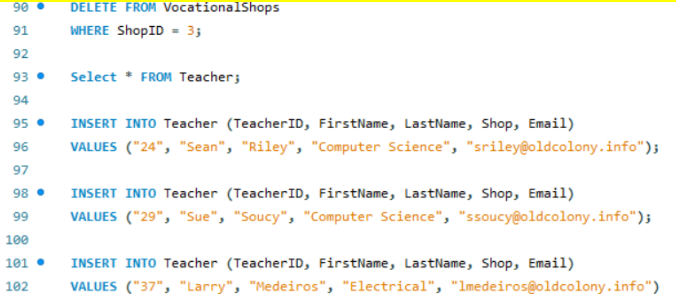
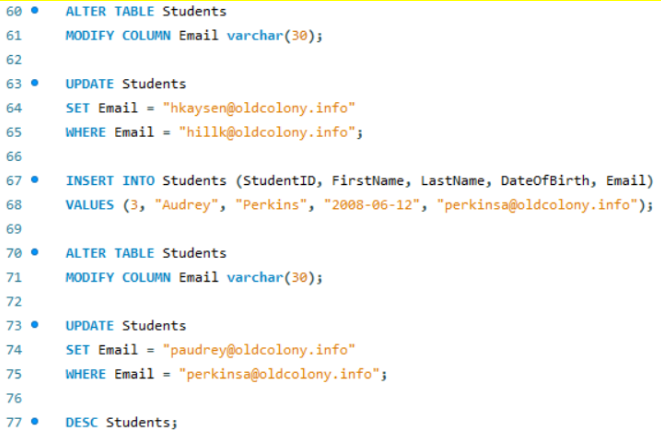
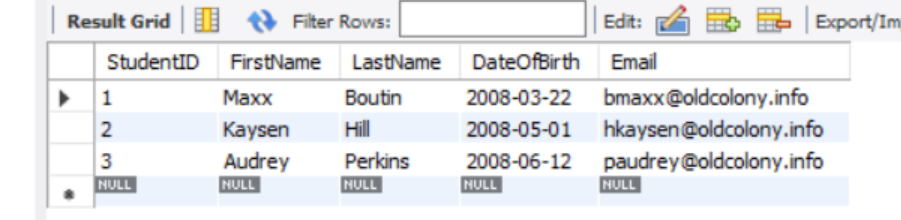
Once these tables were made with their columns made for each section to test the results of the creation of the table, I would then make a couple of SQL lines for each of the tables, giving example data for each of the column categories in the specific tables. Once inputting the data into the tables so they’re all filled, I then altered some of the tables to show how alterations can be made, as well as modifying certain columns.
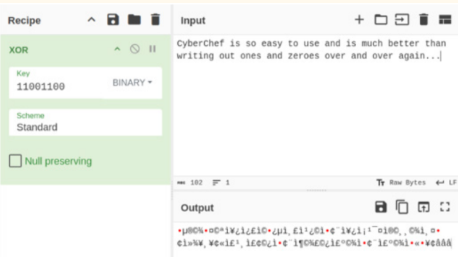
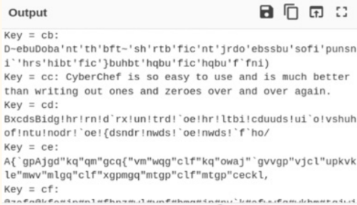
This assignment shows an amazing example of how encrypting messages or passwords can be done. Not only this, but it also displays brute force and how it is used. The brute force example that was given shows how a system could be broken into using this method. This method is performed by attempting every single combination to find the key that would present the text in the correct context.
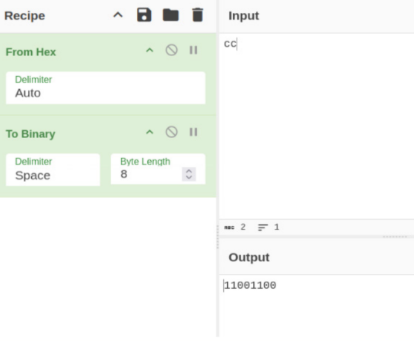
How are these phrases/passwords or whatever text is, encrypted with these keys? This can be performed by inputting a key like a hex number and converting your number into binary. Once this is done, it uses a scheme to encrypt the messages, giving you a result. This result is your encrypted message.
This assignment taught me how to encrypt and decrypt passwords or files to protect them from being attacked or taken. It also showed me how easy it is to decrypt messages even if you thought that they were encrypted and safe.